What's in this post...
![]()
Last Updated on July 22, 2020 by Graham Walsh
The Microsoft Teams Admin Center for MTRs (Microsoft Teams Rooms) is now rolling out. After being previewed at Ignite 2019, it entered a preview earlier this year and I have been lucky enough to be testing with it and providing feedback to the Microsoft product group.
Who can access the Teams Admin Center and control devices?
If you are an admin for your Microsoft tenant, then you will be able to view the TAC and see Teams Rooms under Devices by browsing to https://admin.teams.microsoft.com. Full documentation is available here from the Microsoft Docs site.

However, if you do not want to manage your devices and let one your of partners/suppliers manage them, this is possible with delegate access. This means you can allow another organisation manage your tenant. Full details here. You could also create a new login for someone and just allow them to access to Teams. Details on the roles available are detailed here. You would have to assign them Teams Service Administrator Role, which allows access to devices. This is done via your Azure AD Portal as shown below.

Viewing Device Status
Now we have access to the portal, with the latest Microsoft Teams Room (MTR) software version 4.5.33.0, the devices will auto enrol into your tenant. If for some reason you do not want your devices in your TAC, you can configure the MTR with an XML file. The full guide to using an xml file is available here.
<SkypeSettings>
<DisableTacCommunication>True</DisableTacCommunication>
</SkypeSettings>In the overview pane, we can see all our systems, their status, manufacturer, model and how long it has been offline.

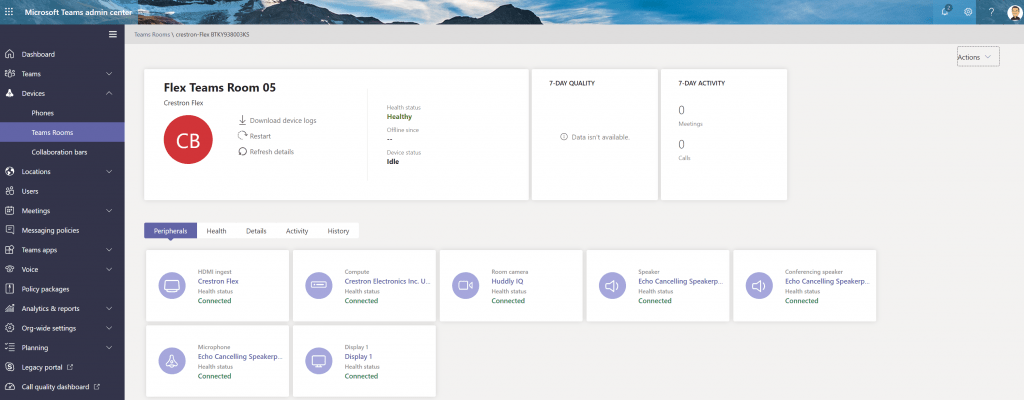
Once we click on a Teams Room name, we can see the further status of the device. From here we can see the status of all the connected devices/peripherals (1). If one is not connected, such as a display or camera, it will show as Unhealthly. When you have two displays (2 and 3), it shows the status of each one. Also on this home screen, you can see the device status (4), so will show if you are in a call, the room’s 7 day call quality (5) and activity (6). From here, the admin can also download the logs from the devices (7). The clever bit here is that it downloads them to the TAC, so you can down to your device when you are ready. Finally you can schedule a restart of the device as well (8). If you select restart now, it will do that in a few minutes, regardless if it is in a call or not. This was fed back during testing and it’s noted in the docs site.

We can then look at the health tab and see the status of the MTR app. In the Peripheral health, we can see that all the devices are connected as per the first screen. Secondly, we can see that status of the Network along with the account elements that make up a MTR account, ensuring everything is signed in OK. Finally we see the build version of Windows and MTR app that the system is running.

In the Details tab, we can see the device manufacturer and model, along with the local IP and the OEM Serial Number / MAC address if that has been written to the BIOS.

In the Activity tab, this is where we can see the past calls for the MTR. You are able to click on a date and drill down into this activity.
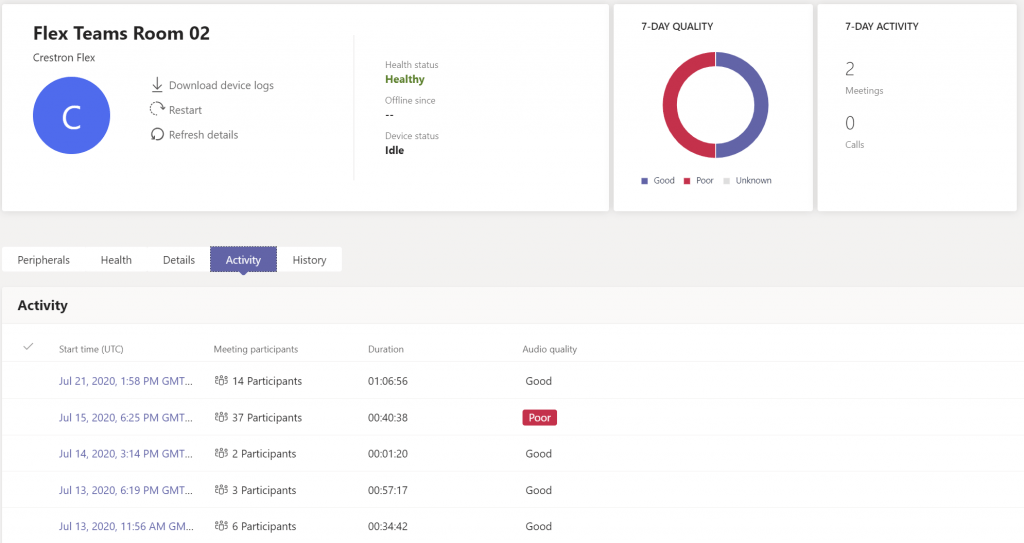

You can then drill down further again and view the overview as see here below and then you have Advanced and Debug level of details.

The screenshot below shows the Advanced details of this call. I also have the option to Export the log in the top right. This will bring down a CSV file.

We can then look at Debug level. This goes on for ages, so here’s a snipped.

The final tab for monitoring the device is History. This shows when a device config was updated (next section) and when a device was restarted.

Device Configration
The main feature of the TAC for the MTR systems is the ability to make some configuration changes remotely, rather than having to visit the device or configure it remotely or locally with the XML config file. When you are on the home page of a device, over in the top right is an Actions menu. Drop this down and you have Edit Settings and Block device. Block device will stop the system report into the TAC. Same meaning as the XML config mentioned earlier. You can also unblock a device too.

In the Edit settings option, this opens up a right hand pane. In the first section Account, you can change the support meeting mode, enable/disable Modern Authentication. What you are unable to do at the moment is set the password for the device. A nice feature is that you can bulk edit the devices too.

In the meeting settings, you can enable/disable Automatic Screen Sharing. This is for during meetings. Outside of a meeting, presentation will start automatically. The Show Meeting name feature is where it can show the title of the meeting. If you have a room that is confidential and you don’t want users seeing the subject of the meeting, disable this and it will just show the organiser. The Auto-leave if everyone else left the meeting is a new feature in 4.5.33.0 which I’ve covered in this blog post.
Under the Devices settings, this allows you to enable/disable dual screen mode and it allows you to replicate you content onto both screens when presenting outside of a meeting. The Bluetooth beaconing allows your Windows 64bit client, Android or iOS device to walk into a room and start the meeting from your device and add the room without touching the centre of room console. I have an overview on this here which includes a video overview.

Finally, we have the Peripherals and Theming section. The peripherals allows you change the speakers and mic that the system is using during Teams calls. The Theming section allows you to change the theme. Unfortunately it does not allow you to upload a custom theme today. That still needs to uploaded to the LocalState folder as described here.

Once you’ve made a change, you’ll most likely have to restart the system. You can restart the system from the Teams Admin Center as mentioned aboved.
Video Demo
There is also a video overview of the Teams Admin Center done by Michael Tressler from Microsoft.
Any questions, let me know below.