What's in this post...
![]()
Last Updated on October 10, 2018 by GrahamWalsh
So since version 16 of Pexip Infinity, it has supported deployments in GCP. The one nice thing about GCP is that the data centres are connected to each other, so you can do a global deployment without having to spin up your own VPNs and pay extra for them.
Anyway, onto the deployment. The official docs are here from Pexip https://docs.pexip.com/admin/gcp_guidelines.htm.
With GCP, you can get $200 of free credit to test it out, so you can sign up with say your Google account that you may already have.
Step 1 – Sign in/register for GCP
Navigate to https://console.cloud.google.com
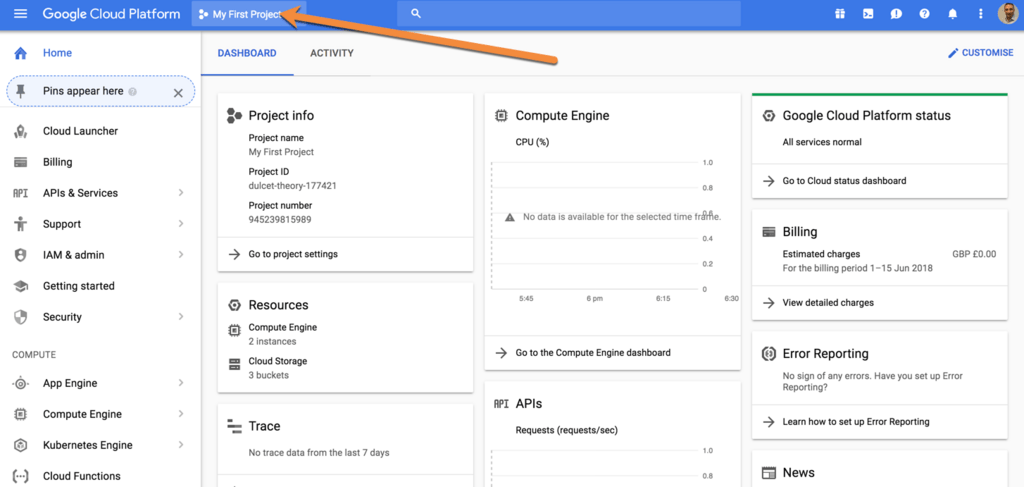
Step 2 – Create a new project
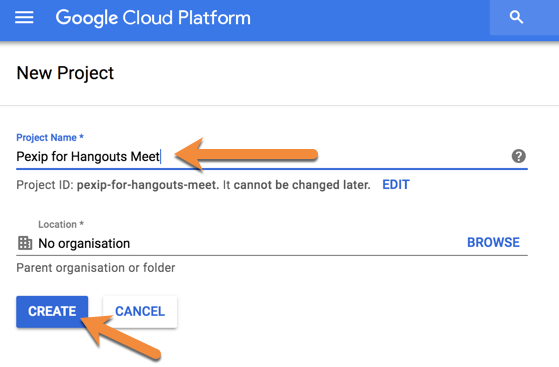
Step 3 – Name your project
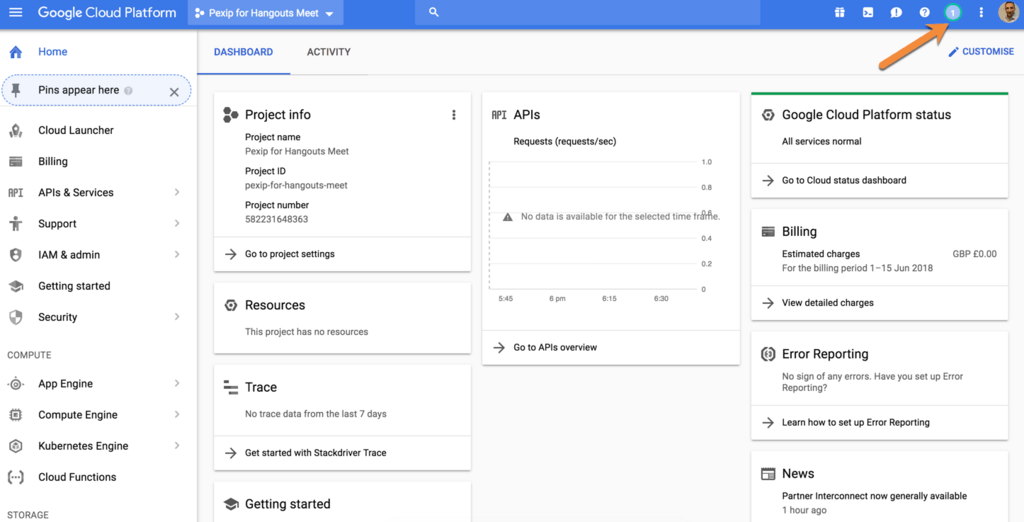
And select Create. You will then see it create your new project in the top right hand side
And you can click on that to see the status
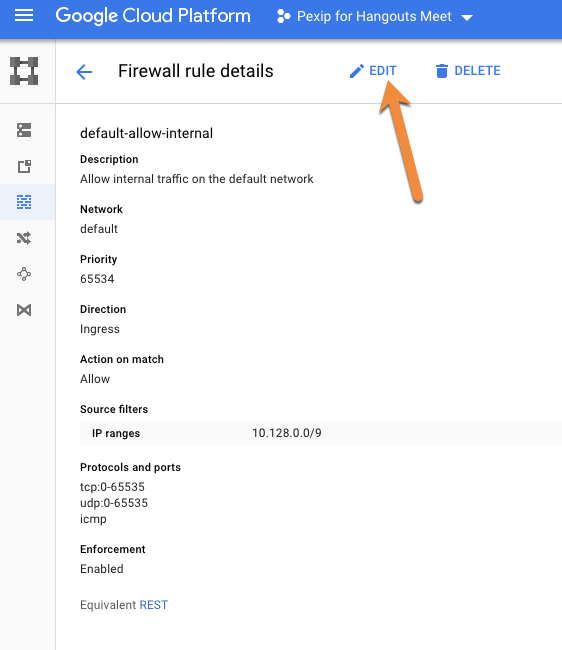
Step 4 – Create Firewall Rules
Navigate on the left hand side menu and VPC Network and then Firewall Rules
Click on default-allow-internal to edit this and then click Edit.
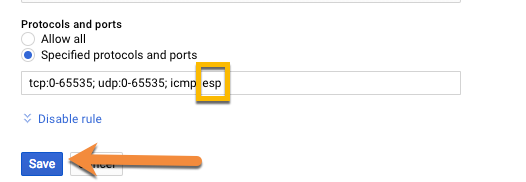
In the editing page, add esp to the allow protocols and click Save. So it should look like this:
tcp:0-65535; udp:0-65535; icmp” to “tcp:0-65535; udp:0-65535; icmp; esp
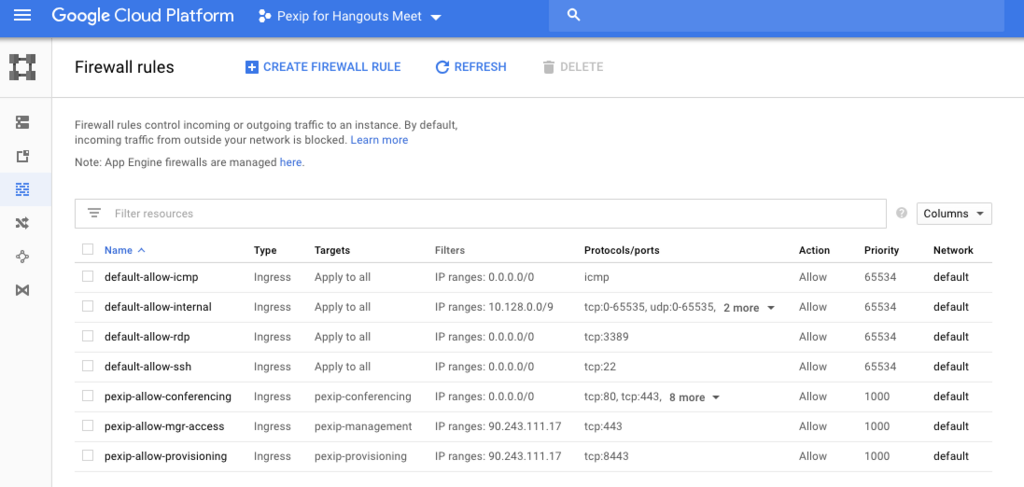
Then create three new rules, pexip manager, pexip provisioning and pexip conferencing. Crete a new rule and enter the details as highlighted below and click create.
Pexip Management
In the source IP range, you can limit this to your network, or leave it open so you can access it from anywhere.
Pexip Provisioning
As above, decide on the Source IP if you want to limit access.
Finally, add another rule for the Pexip conferencing node
For this rule, the Source IP will need to be open, 0.0.0.0/0 so that the conferencing node is available to everyone when doing video calls. The ports are required are:
tcp:80; tcp:443; tcp:1720; tcp:5060; tcp:5061; tcp:33000-39999; tcp:40000-49999; udp:1719; udp:33000-39999; udp:40000-49999
Final overview of the new rules
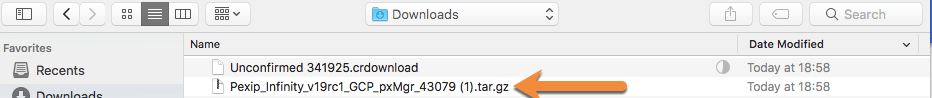
Step 5 – Download the Pexip Management Node & Conference Node Images
You can download the latest release from here. Make sure you use the latest version that is available on the Pexip download site.
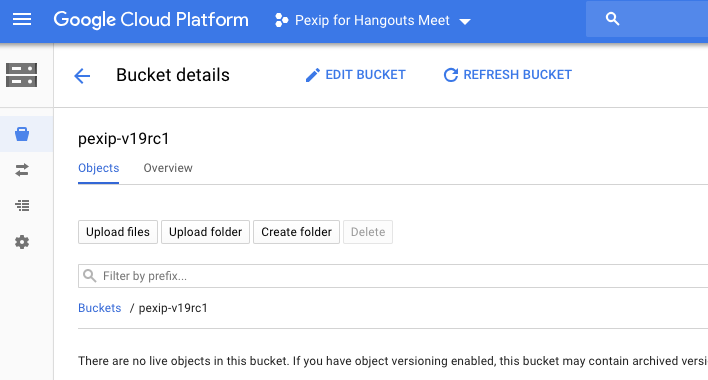
Step 6 – Upload the Images to your GCP Platform
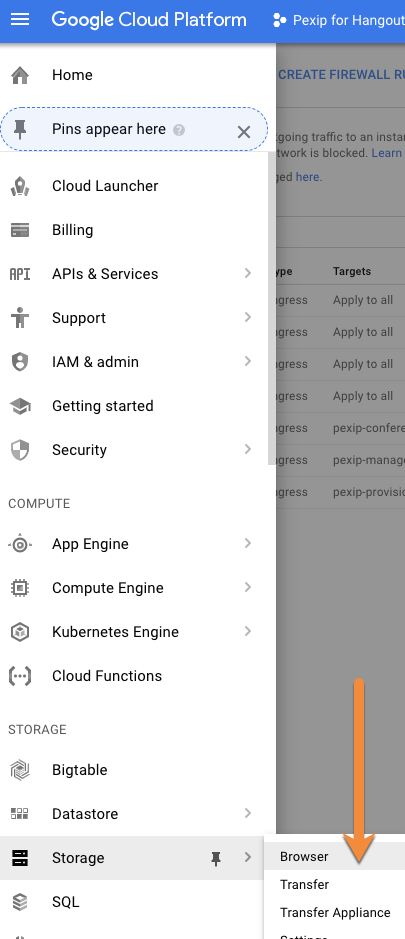
Navigate to Storage > Browser on the left hand side to upload the files
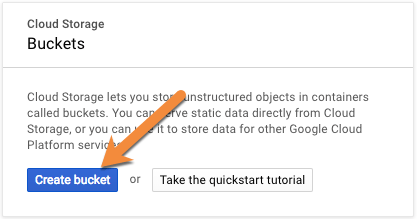
Then Create Bucket and give it a name and select Create
Next click on Upload Files
Select your file that was downloaded
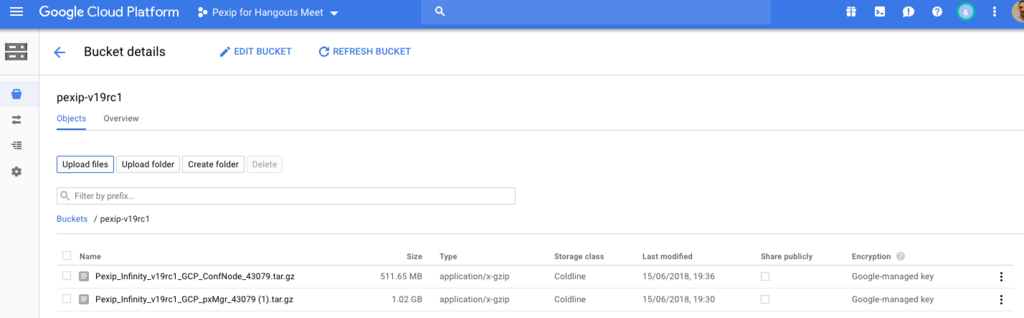
The file will start uploading. You can then upload the conferencing node at the same time as you are allowed to upload multiple items.
Once the files are uploaded, you will see your images uploaded and ready.
Step 7 – Creating the Virtual Machines
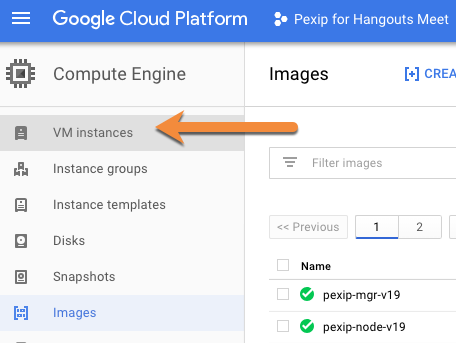
Now we need to navigate to Compute > Compute Engine > Images
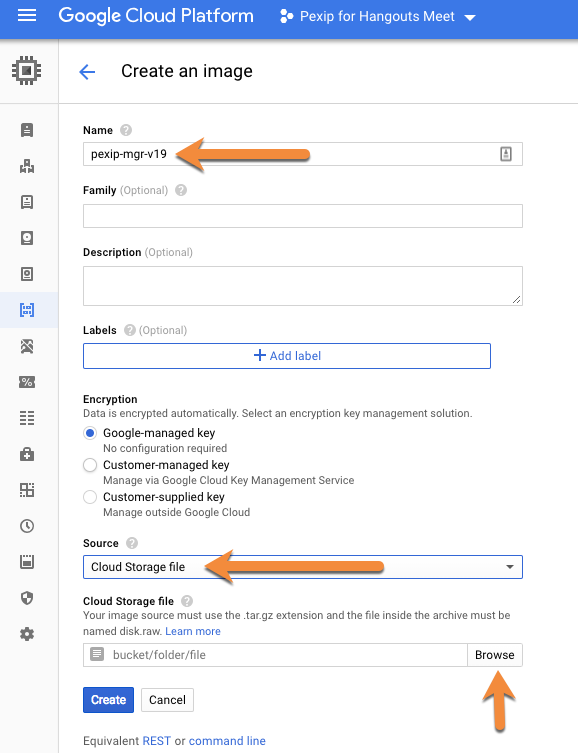
Now click on Create Image
Then enter a name for the VM and set the source as cloud storage file and choose browse.
Now browse for the appropriate file relating to the VM you want to create, it is always good do the management node first.
Once selected, then select Create.
Now do the same for the conferencing node image.
Now you will have your two images ready to build the actual Virtual Machines.
Step 8 – Creating the Virtual Machines
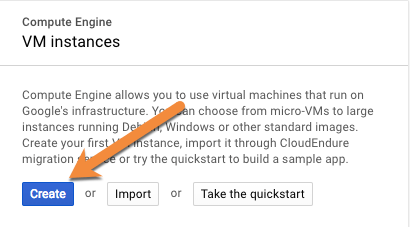
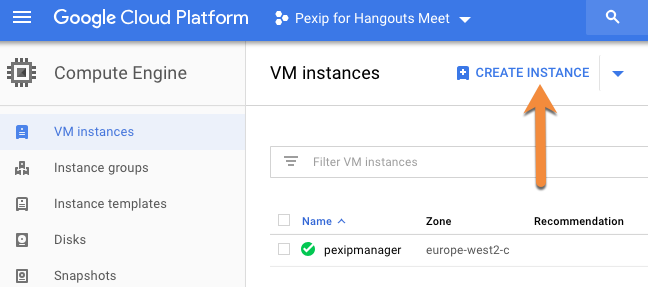
Now navigate Compute > Compute Engine and select VM instances and select + Create Instance from the top.
Click Create on the pop up.
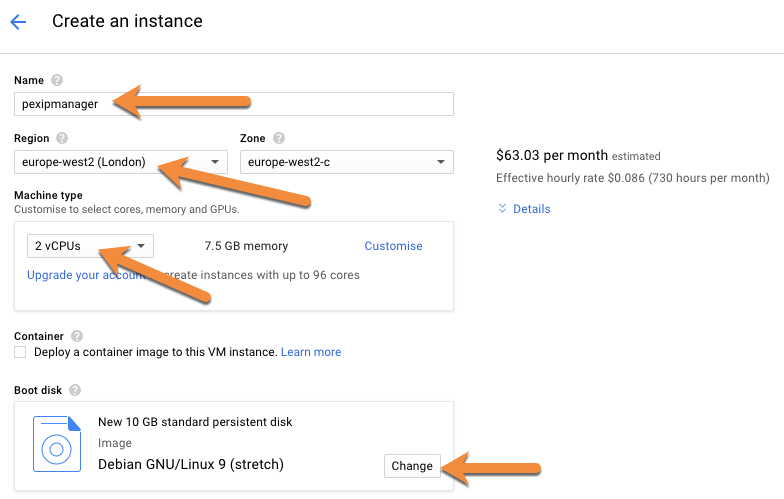
Now give the VM a name, select your region and zone. For the management node, 2 vCPUs is fine. Then select Change under Boot Disk.
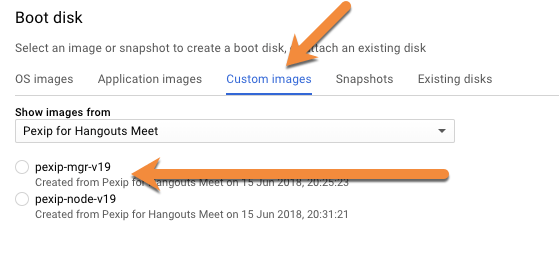
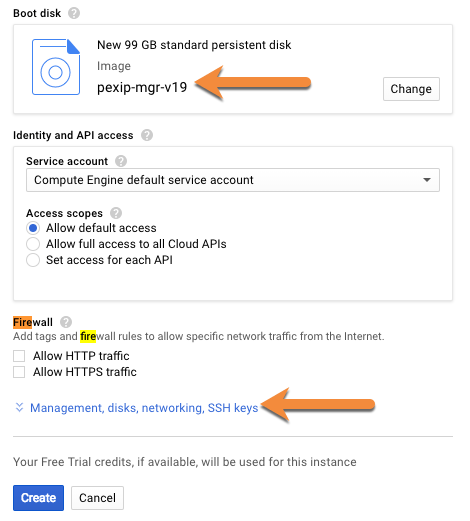
Now select Custom Images and select the Pexip management node that was uploaded to your bucket. For a lab/POC, you can use the standard persistent disk. if going into a production environment, I would recommend SSD disk, so the logs etc can be accessed quicker.
Next select Management, disks, networking, SSH Keys to expand that section.
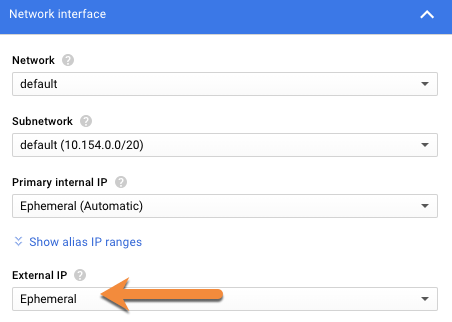
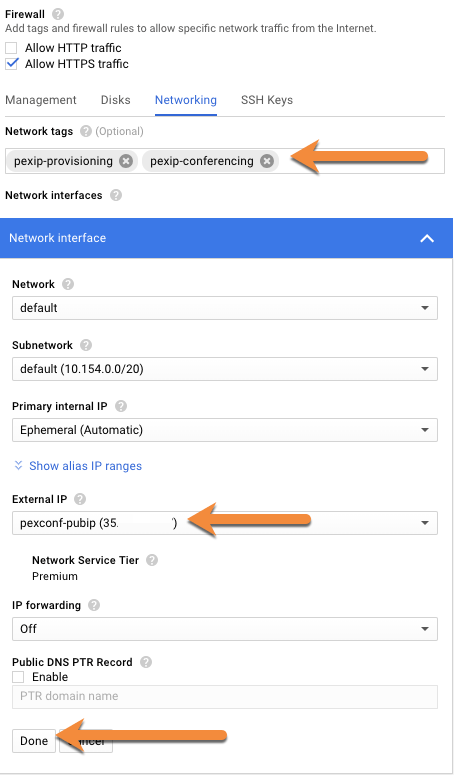
Insert the network tag that matches what you created earlier and then click on network interface to expand that section.
Select Ephemeral under the External IP section to expand the selection.
And select Create IP Address
Just type in a name for your IP address and select Reserve.
Finally, click Done.
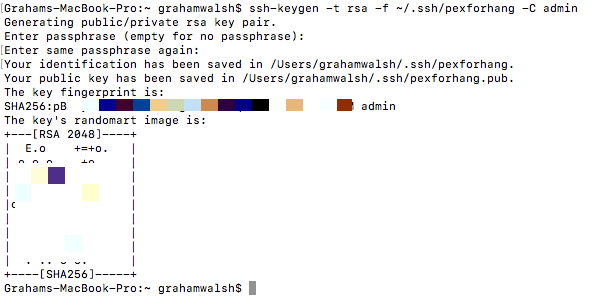
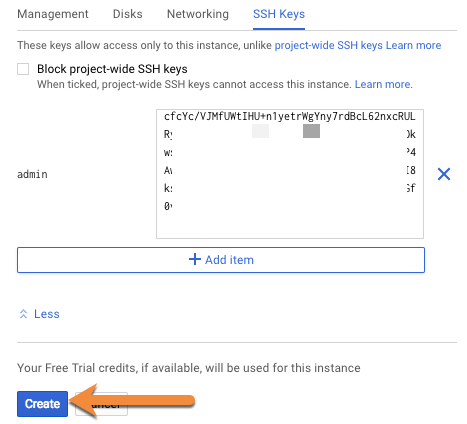
We now need to create SSH keys to access the platform securely once it has booted up
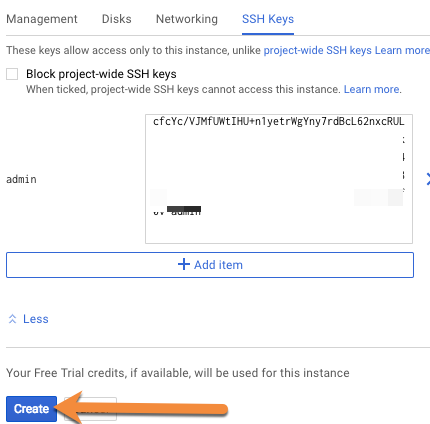
Click on project wide SSH Keys and you can use this guide to create a SSH key for your deployment, depending on what OS you are using
Then create the key as per the guide. Make sure you use the username of admin
Once you’ve created your key, you need to find it and paste the contents of the .pub file into the box (just open it in a text editor).
Then click Create once you’ve pasted it in.
Step 9 – Initial Pexip Infinity Configuration
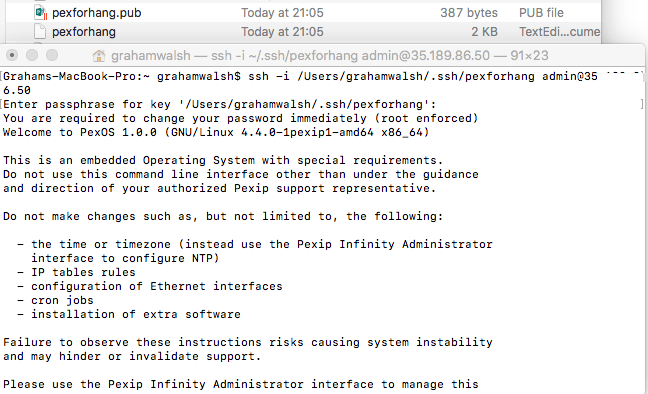
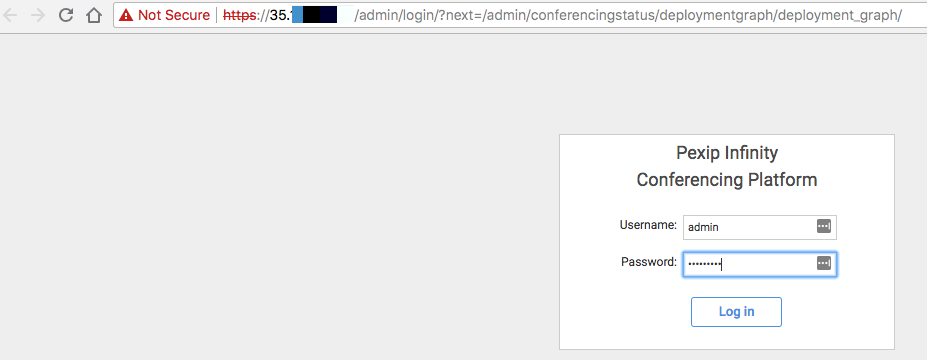
Once the VM has started up, you can now SSH into it to carry out the basic config. To do this, you will need your private key to authenticate it. For me, on a Mac, I use ssh -i (drag in the private key) admin@IP. You will then be asked for your private key password.
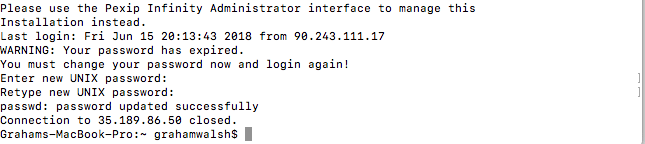
On your first time that you login to Pexip Infinity, you will be asked to create a password and confirm it again
Once logged in, you can now provide the basic networking details. Most of the defaults will be populated in [brackets] so you can just press enter to accept the default detected. If you want to check the Default Gateway, you can do that here.
| Item | Value |
|---|---|
| IP Address | IPv4 Address (use default value) |
| Subnet Mask | Use default value |
| Gateway | Use default value |
| Hostname | Hostname of the management node |
| Domain suffix | Domain name |
| DNS Servers | Use default value unless you have a private network with DNS |
| NTP Servers | Use default value unless you have a private network with NTP servers |
| Web Username | Default username of the local user account |
| Web Password | Enter a password that will be used for this web account |
| Confirm password | Enter the password again |
| Incident Reporting | This is optional. If enabled, it will send a crash alert to Pexip and they will then request a snapshot of the platform to see what might have gone wrong. |
| Deployment & Usage Stats | These are anonymous stats sent to Pexip on what protocols are in use etc. |
Once you have completed the wizard, the management node will then reboot. You can test out connectivity within five minutes by browsing to the public IP address of the management node and using your new credentials.
Step 10 – Creating the Conference Node VM Instance
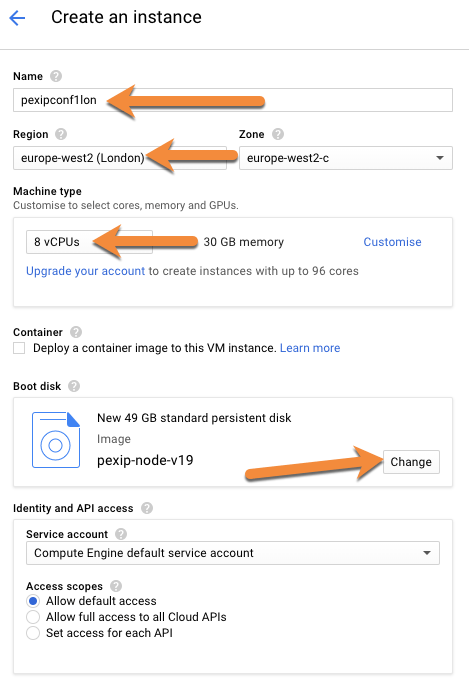
Next up we need to create the conferencing node VM, this is the guy that does all the transcoding of media. Same as previously, give it a name, select the region and zone.
This time we need a more powerful server, so the minimum recommended is 8 vCPUs
Add in the tag of pexip-provisioning too so you can upload the config to this VM over port 8443. Also create a public IP too.
Then you can add in the same SSH key and then click Create
Once the VM has been created, you should see both VMs running now with their Public IP Addresses.
You can now log into the management node again.
Step 11 – Creating the conference node
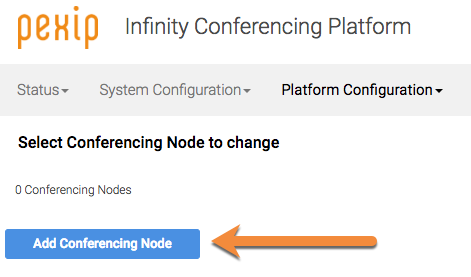
Once logged into the management node, navigate to Platform Configuration > Conferencing Nodes and then click on Add Conferencing Node.
In the Deployment Type, select Generic as we will apply the configuration to the vanilla conference node we have spun up.
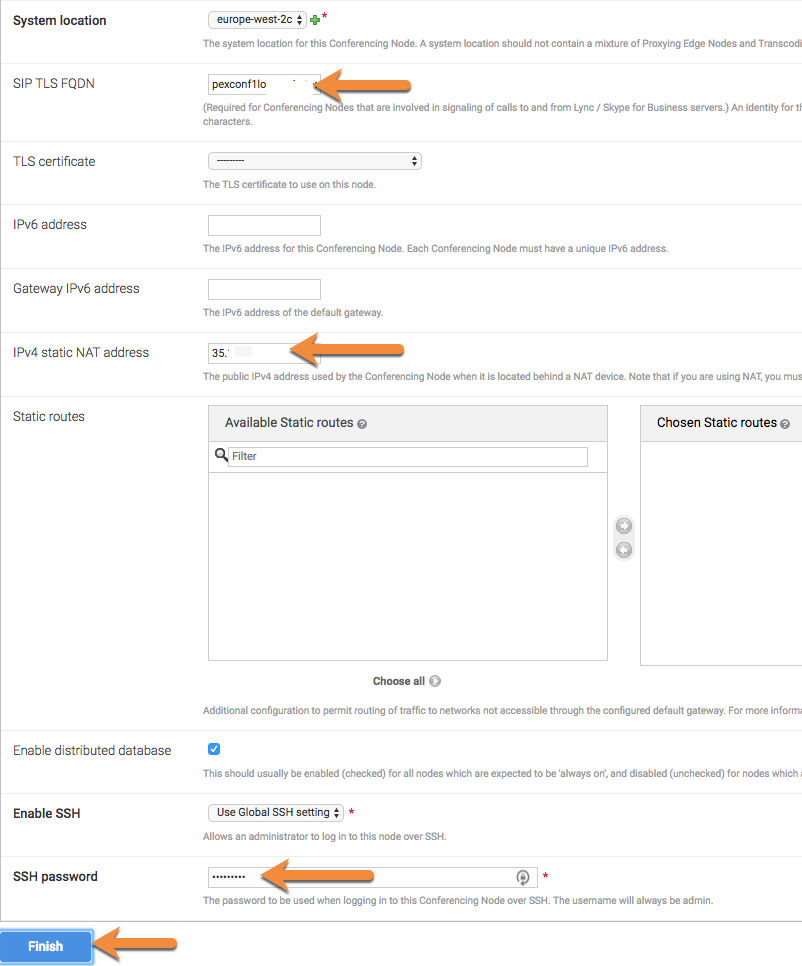
Now fill in the areas highlighted, using the details from the VM in GCP for the IP addressing details.
Next we need to add a System Location. Click on the + and then fill in the details as shown below.
For the SIP TLS FQDN, this is the FQDN of this conference node. Also add in the Public IP address of the Conferencing Node in the Static NAT address box. Also enter a password, so that you can SSH into the conference node if directed by Pexip support. Then click Finish.
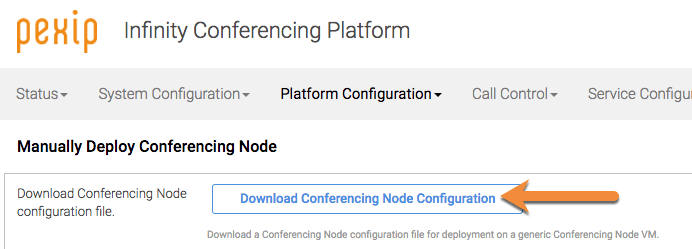
On the next page, Download the config to your local machine. This is just a XML config file.
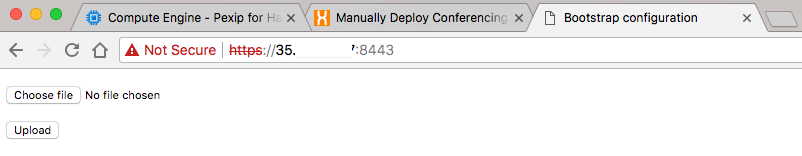
Now browse to the IP address of your conference node on port 8443 and you will be presented with a very simple page. Click on Choose file and select you downloaded XML file and then choose Upload. The server will take the config and reboot.
Step 12 – Checking the Conferencing Node Status
The way Pexip works, is that the management node and conference node check in with each other. If they are not able to speak, then it’s usually a firewall issue blocking the following:
Any internal firewalls must be configured to allow UDP port 500 and traffic using IP protocol 50 (ESP) in both directions between all Pexip nodes.
If everything is ok, then the conference node will book and check in. You can see this in the Administrator log.
If you browse to Administrator log, you will see Started performance sampling. This means two things. You have configured the firewall correctly and that the conference node is now doing a sample to see what capabilities it has in terms of the number of HD calls available based on the underlying CPU architecture.
Once this is finished, you will see the output if you refresh the screen.
Now if you head back to home screen, Live View, you will see a happy conference node.
Step 13 – Making a test call
Pexip Infinity has a built in Test call service. You can see the settings under Service Configuration > Test Call Service
You can then add other alias such as testcall, or just test etc. I have added in the full SIP URI so that it can be called from any SIP device.
Then click save and wait one minute for it to apply the changes. Any changes you make in Pexip, you must allow one minute.
Now you can navigate to the IP address of the conference node and you will be presented with a first time welcome screen asking for your name and access to your camera and microphone.
You will know of that has worked as you will see your local preview.
Now press the Call button and type in testcall (one of the alias’s created earlier).
As you will see below, I have a successful call as I can hear the audio error and I can see the invalid license image. If the platform was licensed, I would get a three step process of checking my audio and video.
Step 14 – Setting the SIP TLS FQDN
This is required when using the Pexip platform and integrating with say Skype for Business. Navigate to Platform Configuration > Global Settings and then in Pexip Infinity domain (for Lync/Skype for Business integration) enter your SIP domain you are using for your Pexip deployment such as vc.company.com.
There you have it, you have a completed Pexip Infinity deployment in the Google Cloud. In the next blog post, I will detail how to get a public SSL certificate for 90 days for free from ssl.com so that you can fully test the platform.